Security Fix for Directory Traversal - huntr.dev #2
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "418sec/master"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
https://huntr.dev/users/alromh87 has fixed the Directory Traversal vulnerability 🔨. alromh87 has been awarded $25 for fixing the vulnerability through the huntr bug bounty program 💵. Think you could fix a vulnerability like this?
Get involved at https://huntr.dev/
Q | A
Version Affected | ALL
Bug Fix | YES
Original Pull Request | https://github.com/418sec/quickserver/pull/1
Vulnerability README | https://github.com/418sec/huntr/blob/master/bounties/npm/quickserver/1/README.md
User Comments:
📊 Metadata *
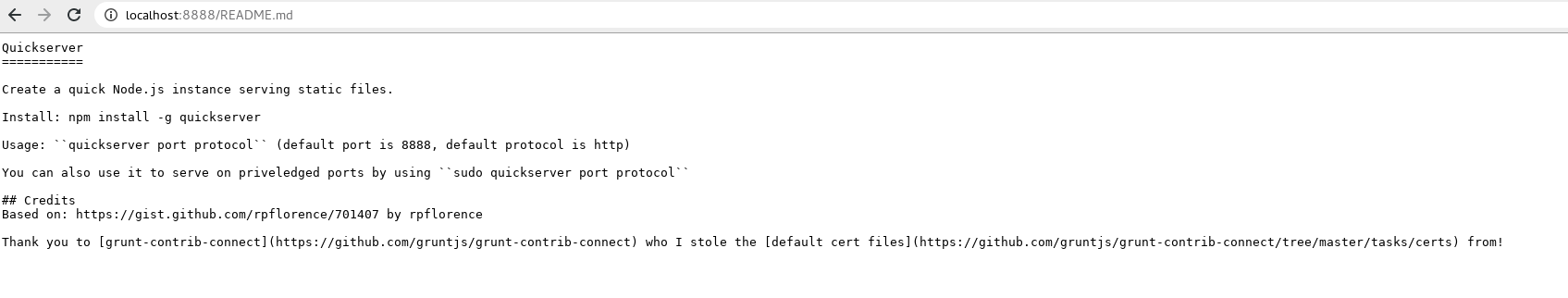
quickserver is Quickly start a Node.js instance serving static files,
this package is vulnerable to Directory Traversal, which may allow access to sensitive files and data on the server.
Bounty URL: https://www.huntr.dev/bounties/1-npm-quickserver
⚙️ Description *
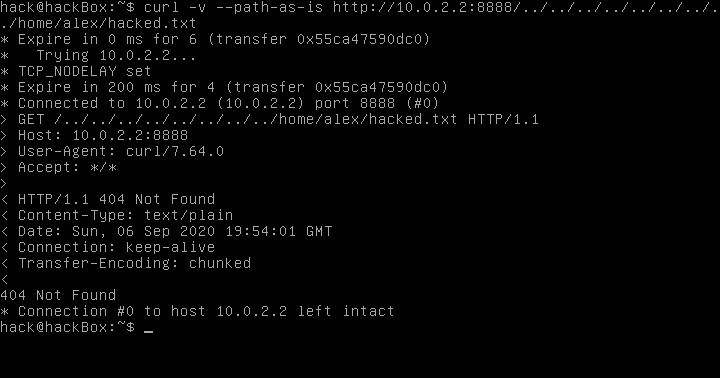
There is no path sanitization in the path provided making quickserver vulnerable against path traversal through the ../ technique, leading to information exposure and file content disclosure.
💻 Technical Description *
Fixed by sanitizing any occurrence of ../, using regexp.
🐛 Proof of Concept (PoC) *
./bin/quickservercurl -v --path-as-is http://127.0.0.1:8080/../../../../../../../../../../../etc/passwd🔥 Proof of Fix (PoF) *
After fix Response code 400 Bad request is returned to user instead of restricted file content
👍 User Acceptance Testing (UAT)
After fix functionality is unafected
View command line instructions
Checkout
From your project repository, check out a new branch and test the changes.Merge
Merge the changes and update on Forgejo.Warning: The "Autodetect manual merge" setting is not enabled for this repository, you will have to mark this pull request as manually merged afterwards.